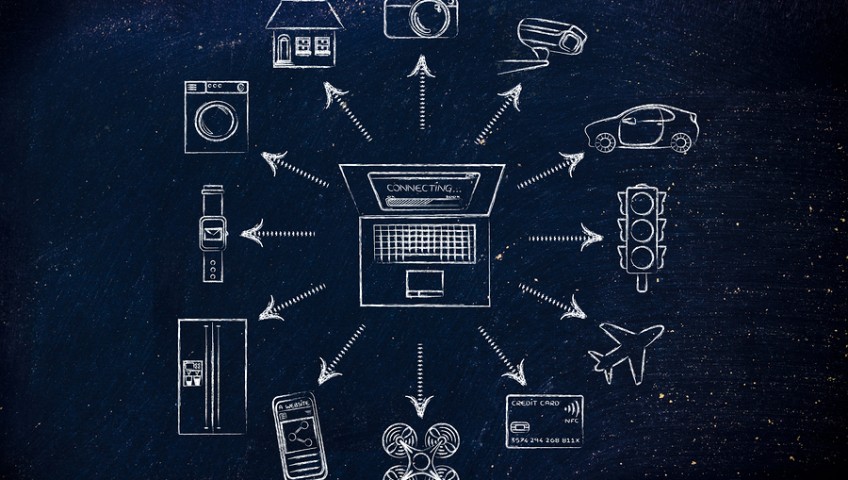
Can your smart coffee maker hack into your server? Consider this: your smart coffee maker at home (or at the office) is likely connected to the same network you use for your computer. If a bad guy can get to your coffee maker, he can get to your network. Be aware of the business risks from the Internet of Things (IoT).
In a typical office setting, your printers and security cameras are internet-enabled. Of course, your computer network is, too. Ideally, your IT provider is coordinating with the security company, phone provider, and other vendors to keep your network secure.
But what happens at home? Smart devices like Amazon Echo, video-enabled door bells, and yes, coffee makers, are connected to the internet. These devices can be a threat to your network if they lack strong passwords, are poorly programmed, or don’t get updated.
With unsecured smart devices, you could unknowingly infect your work laptop just by using your home network. Then, it could infect your work network when you return to the office. Keep this in mind as you add internet-enabled devices at home.
The National Cyber Security Alliance recommends following these tips to enjoy the benefits of cutting-edge tech with more peace of mind:
- Learn how to safeguard your IoT devices: Protecting devices like wearables and smart appliances can be different than securing your computer or smartphone. Research how to keep an IoT device secure before you purchase it. Then, take steps to safeguard your device over time.
- Pay attention to the Wi-Fi router in your home: Use a strong password to protect the device and keep it up to date. Name it in a way that won’t let people know it’s in your house.
- Delete when done: Many of us download apps for specific purposes or have apps we don’t need any more. It’s a good security practice to delete apps you no longer use.
- Own your online presence: Understand what information your devices collect and how it’s managed and stored. Set the privacy and security settings on devices to your comfort level for information sharing.
- Research before you buy: Before adopting a new smart device, do your research. Make sure others have had positive experiences from a security and privacy perspective.
- Lock down your login: Fortify your online accounts by enabling the strongest authentication tools available, such as biometrics, security keys or a unique one-time code through an app on your mobile device. Your usernames and passwords are not enough to protect key accounts like email, banking and social media.
To learn more about how CRU Solutions can help reduce your business risks from the Internet of Things, contact us.